Sebo 5010AM Brush Roller for X4, G1, FELIX1, K3, ET-1 and D4 Vacuum | Davy jones, Amigos de la mano, Linux
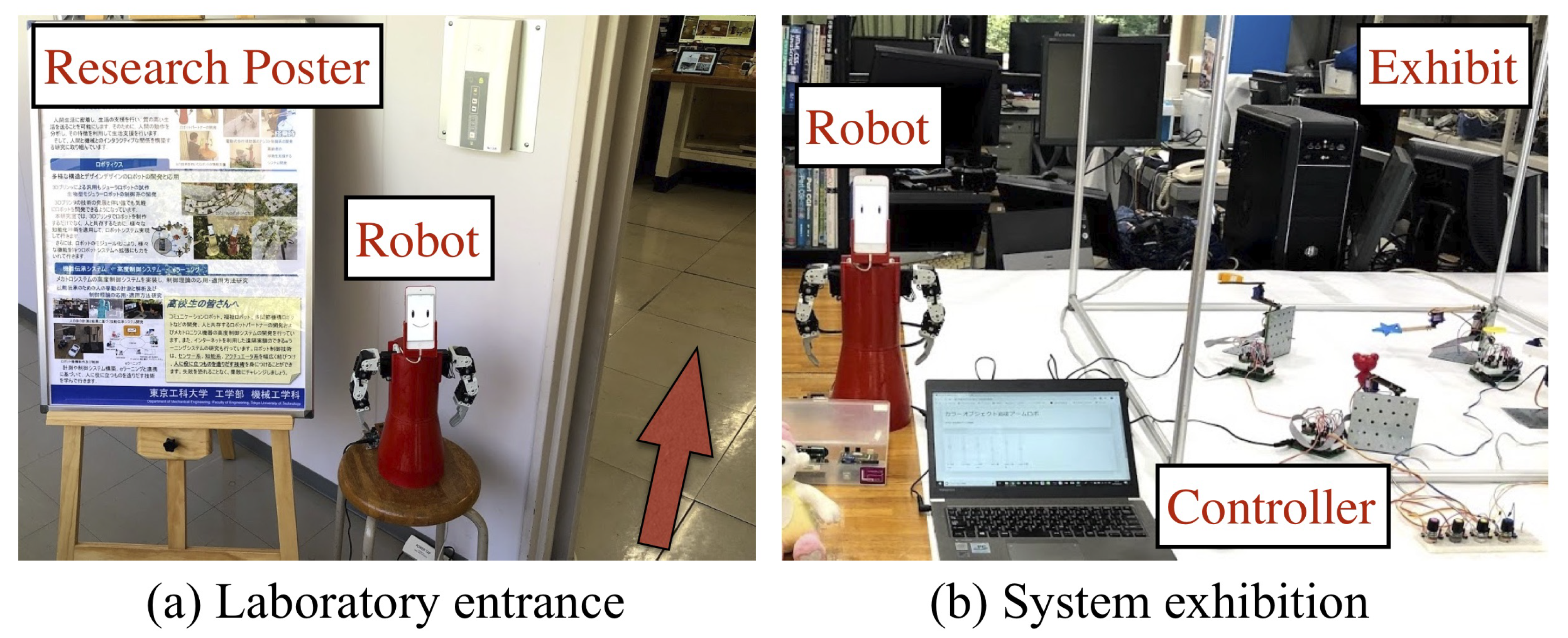
Applied Sciences | Free Full-Text | Robot Partner Development Platform for Human-Robot Interaction Based on a User-Centered Design Approach | HTML

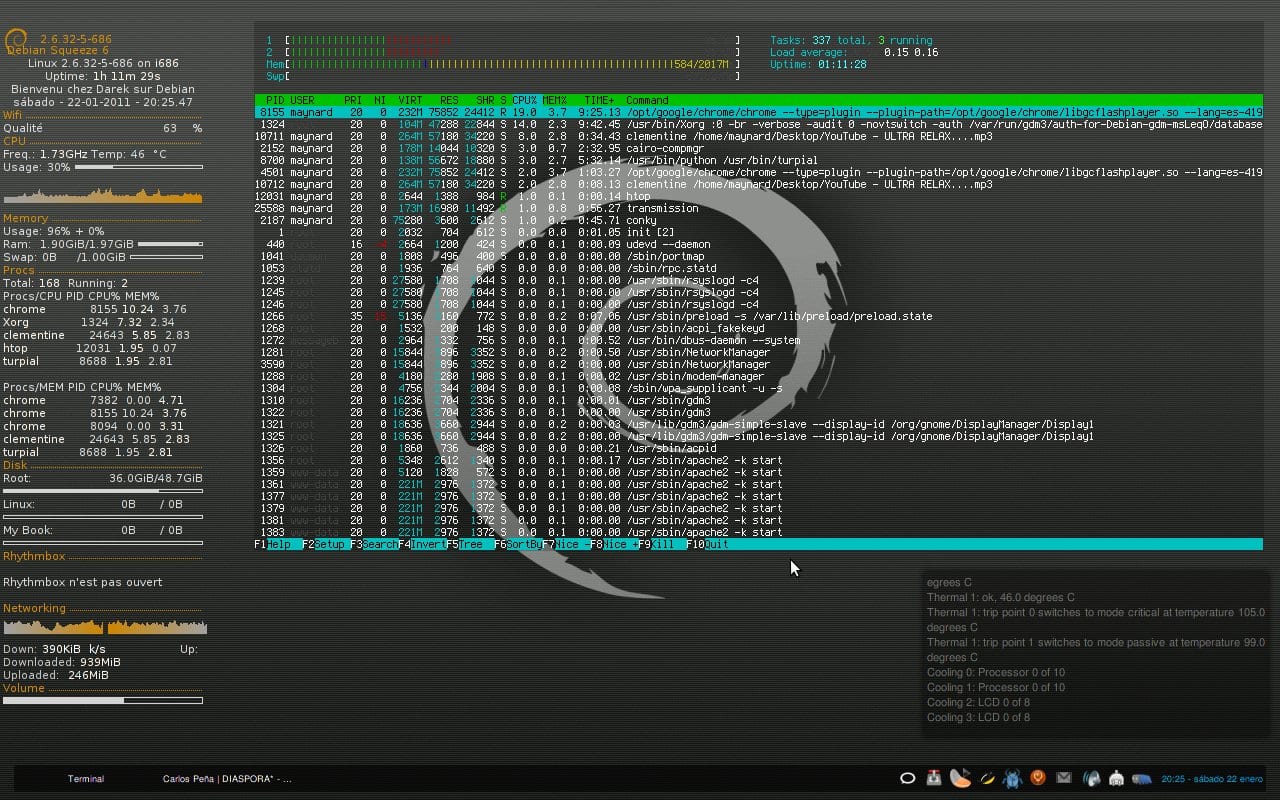
Linux on IBM System Z: Performance Measurement and Tuning: IBM Redbooks: 9780738436326: Amazon.com: Books
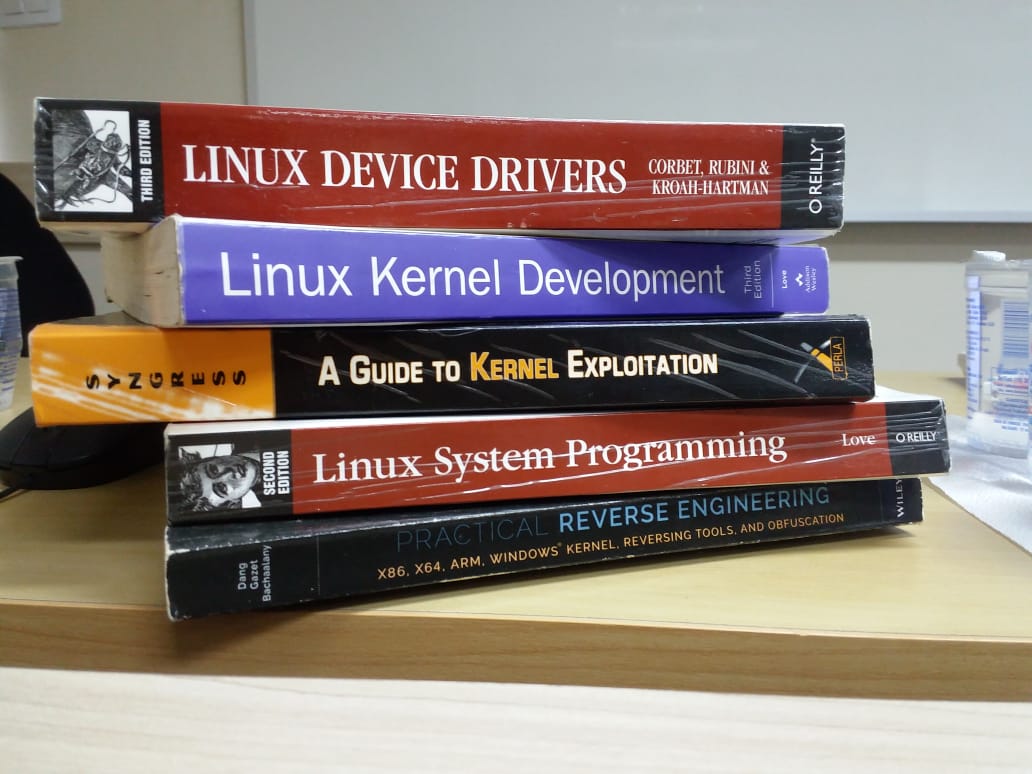
Laios Barbosa on Twitter: "Coordinating a Linux Kernel Exploitation training ;) #gohacking #kernel #exploit #PenTest https://t.co/eK9UuHm1Sx" / Twitter
linux-intel-lts-xenomai/MAINTAINERS at F/4.19.59/base/ipipe/xenomai_3.1-rc3 · intel/linux-intel-lts-xenomai · GitHub

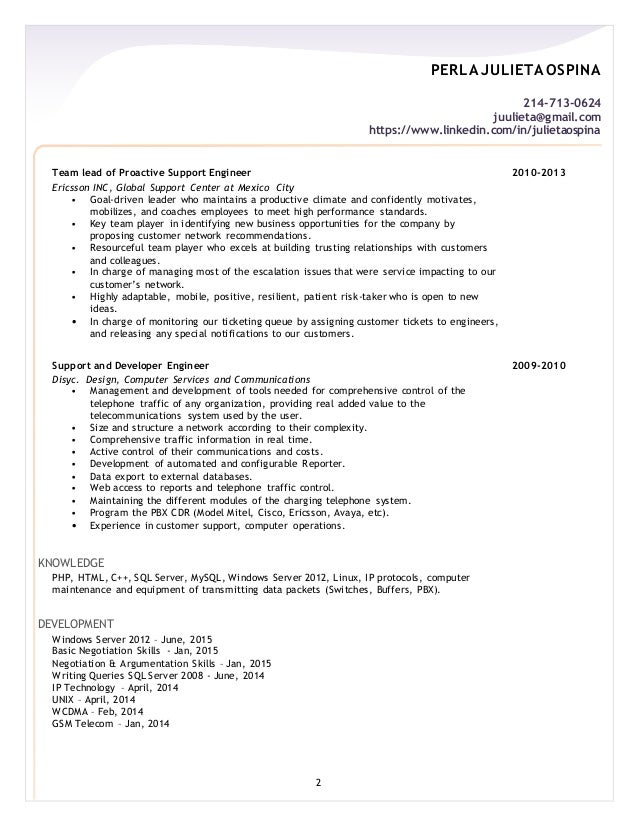
Amazon | Kernel Hacking: Exploits verstehen, schreiben und abwehren: Schwachstellen in Kernel-Architekturen erkennen und Gegenmassnahmen ergreifen | Perla, Enrico, Oldani, Massimiliano | Client-Server Systems